So, you just got a call from a friend who said that they went to your WordPress website on their iPad but it’s showing porn instead of your business’ regular page. Well, isn’t that special?
There have been a rash of these events lately. Sucuri, a website that helps people detect hacks and clean up their websites afterwards, even stated that their detection software is having a hard time finding these new hacks.
So, when a professional hacker detector can’t find it, what are the rest of us supposed to do?
For starters, relax. It’s nothing personal. Most of the hackers don’t even realize they’ve hacked your website. Their automated programs are attempting to hack thousands of websites every day. Yes, they are jerks -- or insert your own, more colorful word if you prefer.
This happened to a website that I help maintain for a small non-profit group just last week. The desktop computer version of the website showed no problems at all. And, like Sucuri stated on their blog, Sucuri SiteCheck couldn’t find the problem either. However, if you tried to pull up the website on your phone or tablet … BAM. Porn.
Before I show you how I found and removed the malicious code, let’s talk about a few easier ways to handle this that don’t require you to become a computer programmer.
Hire a Hitman
I know you’re angry, but I don’t mean that kind of hitman. I mean bring in a professional service that monitors, prevents, and repairs hacked code.
Even though Sucuri.net couldn’t detect it, they are typically a great option. At only $89 per year, you’ll be glad you hired them if you have to clean up your website yourself. Sucuri’s manual malware scans are free (scroll down on the home page and you'll see the service.) But they don’t remove the malware, they just detect the presence of the it (except in this recent case.)
Other services like iLockout.com and SiteLock.com offer similar services. iLockout is comparable in price to Sucuri while SiteLock runs closer to $30 per month.
Did You Back It Up?
That’s always the first question your IT person asks, isn’t it? A frequent backup schedule is one of your best defense measures as you can restore the backup to a state before the hack took place.
The cheapest solution, though not the easiest to commit to, is to go into cPanel (your administration page where you can install WordPress, create email accounts, perform backups, etc,) create the backups manually, and download them manually. But fortunately you don’t have to do that. Automated backups are the way to go.
Tools like BackupBuddy (currently $80 per year for 2 websites,) Ready! Backup (free,) and UpdraftPlus (also free and very highly rated) are available. Although I don’t currently have experience with either Ready! Backup or UpdraftPlus, I think it’s worth noting that UpdraftPlus is one of the highest rated plugins available for WordPress.
ManageWP also provides automated backup services along with a slew of other great features. It will run you $45/year for a single website using their professional package. It’s definitely worth a look. Watch out for the “standard package,” though. It’s much cheaper but the backups are manual.
Another option, often free, is to check with your host. I use GoDaddy (* affiliate link) to host most of my sites and it has a very nice backup feature. I get a new backup saved to my DropBox account (and, therefore, also saved to my home computer hard drive and then backed up to Carbonite) every week.
Remove the Hacked Code Yourself
When all else fails, removing the hacked code yourself will get the job done. It won’t be a lot of fun and there’s every chance that you could remove some good code. So, back up your website (see above) before you do this. If it fails miserably, restore the backup and try again.
Warning: if you're not comfortable in code, this can be more dangerous to your website than the hackers. Please use caution before proceeding.
I normally download the entire website, search all the PHP files using a text editor, and then clean up the online files using the file manager in cPanel.
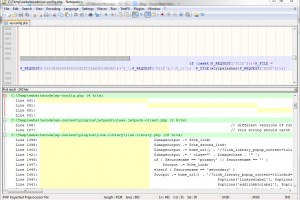
Yellow bars in the bottom panel show instances of 50 spaces in the files. The upper panel, with Word Wrap on, shows the full line of hacked code.
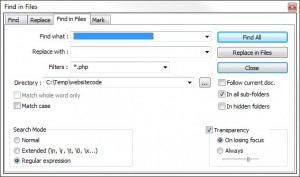
The approach I’ve found to be the most effective is using NotePad++ (free text editor - which is very different from a word processor, please don’t try MS Word) to search through all the PHP files for a few common patterns. One of the quickest ways to find the hacked code is to search for an excessive number of spaces. I usually use 50 spaces and search all files. The hackers like to push the text far off the right-hand edge of the visible document so that as you’re scanning through the files, you don’t see the hacked code. You can also search for excessive numbers of tab characters (used for the same reason, but here I’ll search for about 12) and for the term replace. Be warned, though, that “replace” is used all over your website. You’re looking for code that appears to be encrypted.
If you go this route, please be careful and have a backup ready to restore if things go poorly.
The Quick Takeaway
Remember that hacking isn’t personal. I’ve heard a lot of people ask, “Why would they do this to me?” It’s not you, it’s them. Seriously. Get it fixed and move on with life.
And make backups. Please. One day you’ll be glad you didn’t have to learn that lesson the hard way.
How do you thwart hackers? Or do you have an "I got hacked" story?
Photo Credit: "Anonymous Hacker" by Brian Klug is licensed under CC BY 2.0